In the past two weeks I set up a new VPS, and I run a small experiment. I share the results for those who are curious.
Consider that this is a backup server only, meaning that there is no outgoing traffic unless a backup is actually to be recovered, or as we will see, because of sshd.
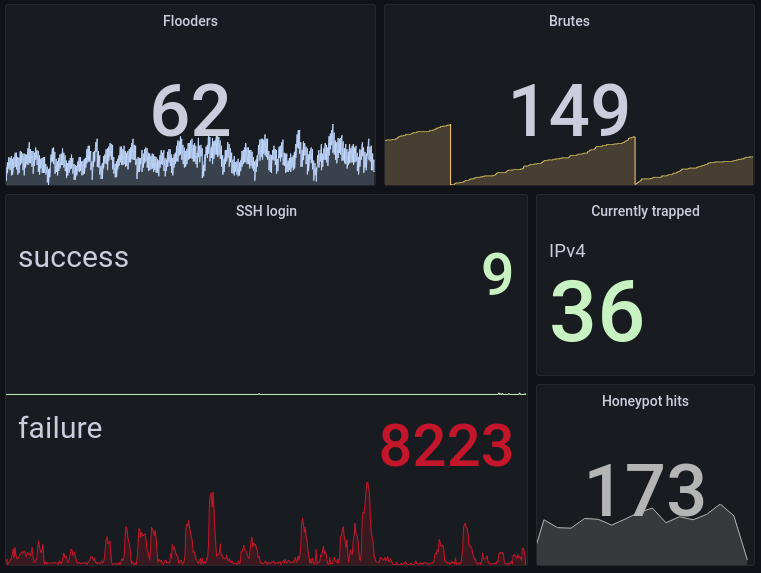
I initially left the standard “port 22 open to the world” for 4-5 days, I then moved sshd to a different port (still open to the whole world), and finally I closed everything and turned on tailscale. You find a visualization of the resulting egress traffic in the image. Different colors are different areas of the world. Ignore the orange spikes which were my own ssh connections to set up stuff.
Main points:
-
there were about 10 Mb of egress per day due just to sshd answering to scanners. Not to mention the cluttering of access logs.
-
moving to a non standard port is reasonably sufficient to avoid traffic and log cluttering even without IP restrictions
-
Tailscale causes a bit of traffic, negligible of course, but continuous.
Acronyms, initialisms, abbreviations, contractions, and other phrases which expand to something larger, that I’ve seen in this thread:
Fewer Letters More Letters DNS Domain Name Service/System HTTP Hypertext Transfer Protocol, the Web IP Internet Protocol SSH Secure Shell for remote terminal access UDP User Datagram Protocol, for real-time communications VPN Virtual Private Network VPS Virtual Private Server (opposed to shared hosting) nginx Popular HTTP server
7 acronyms in this thread; the most compressed thread commented on today has 8 acronyms.
[Thread #42 for this sub, first seen 14th Aug 2023, 15:55] [FAQ] [Full list] [Contact] [Source code]
Good bot!
Great bot
Public key auth, and fail2ban on an extremely strict mode with scaling bantime works well enough for me to leave 22 open.
Fail2ban will ban people for even checking if the port is open.
Yeah fail2ban has worked great for me
Honest question, is there a good default config available somewhere or is what
apt install fail2bandoes good to go? All the tutorials I’ve found have left it to the reader to configure their own rules.If Fail2Ban is so important, why the h*** does it not come installed and enabled as standard?!
Security is the number-1 priority for any OS, and yet stock SSHD apparently does not have Fail2Ban-level security built in. My conclusion is that Fail2Ban cannot therefore be that vital.
You really shouldn’t have something kike SSHD open to the world, that’s just an unnecessary atrack surface. Instead, run a VPN on the server (or even one for a network if you have several servers on one subnet), connect to that then ssh to your server. The advantage is that a well setup VPN simply won’t respond to an invalid connection, and to an attacker, looks just like the firewall dropping the packet. Wireguard is good for this, and easy to configure. OpenVPN is pretty solid too.
You say this and are downvoted.
While we are coming off the tail of Def Con where there where a plethora or small talks and live examples of taking advantage and abusing just this.
Just trying to parse your comment, I assume your first “this” and second “this” are referring to different things, right?
I don’t understand your comment, what you are saying. Could you elaborate a bit, please? I’m interested why it’s a bad idea what previous comment suggested.
Of course I can dig into DefCon videos and probably would do if needed, but perhaps you know what exactly the issue is
The first this means the comment he answered to and the second one means ssh being used as an attack surface, being described in defCon talks
I usually just run a ZeroTier client on my Pi connected to a private P2P network to solve this issue, and then have ProtonVPN over Wireguard for all internet traffic in and out of the Pi.
Or, you know, just use key auth only and fail2ban. Putting sshd behind another port only buys you a little time.
Yeah but the majority of bots out there are going after easy prey. Honestly, if you use public key authentication with ssh you should be fine, even if it is on port 22. But it does of course clog up access logs.
The majority of bots out there are stopped by just using a hard to guess password. It’s not them that you should be worried about.
The majority of bots doesn’t even show up in the logs if you disable password auth in the server config, as you typically should.
I’ve noticed that a lot of the scans these days almost always switch IPs after 2-3 attempts, making IP blocking a lot more difficult.
Let’s say that you could ban for an indefinitely large amount of time after a single failure to authenticate, that’d make them run out of IPs much quicker than you’d run out of CPU/BW, so I don’t really see the issue
Potentially yeah, although a single failure means I might lock myself out by accident.
True, but very unlikely (once your ssh client is configured once and for all), and in that event you can always switch connection (use a data network, proxy, vpn, hop from another server you have ssh access, etc)
I’ll take that tiny amount of traffic telling scanners there’s no password auth over having to remember port settings for ssh, scp and rsync any day.
vim ~/.ssh/configdeleted by creator
My configs remember stuff for me.
Fair point. These logs are only useless chatter anyway for everyone with proper key auth.
For me it’s not about the traffic, more the log spam.
Generally I’ll have :22 enabled internally, and anything non-standard is defined in
~/.ssh/configand shared out so I don’t have to remember things.
I opened a raw text channel on the Telnet port for a personal game engine project and someone tried to enable commands and do some shady stuff. Unfortunately for them, that’s not a valid chess move.
I’d favour own VPN instead of relying on an additional third party
Right? PiVPN is easy AF and uses WireGuard. No reason not to set up something yourself if you’re already selfhosting.
Please ELI5: How does this solution work? You tunnel yourself in your home network with a VPN on your PI? How is that safer, isn’t there still a port open?
I have a port open, yes, but it’s not port 22. The problem with Tailscale is you’re trusting a third party. With my setup, it’s just me connecting directly to my Pi. Thanks to port forwarding the only open port pointing to my Pi is the one that I use for WireGuard.
I already have a DDNS and domain name pointing to my house, so there’s effectively no added risk compared to my existing setup with a couple webapps being reverse proxied behind Caddy on a different device.
Thanks! I think I get too hung up on the VPN-part. If I had a setup where I open one Port to a Pi which is set up as a nginx reverse proxy that redirects the connection to my different services depending on the URL - homeassistant.myserver.com, backup.myserver.com,… - would that be considered a VPN?
Mine is quick enough to run remote desktop over
Same, I use Moonlight/Sunshine to stream my main gaming PC. I can even use wake on lan, so the big chungus isn’t drawing power unless I’m using it.
Oh, something new to try, thanks
Do you have any tutorial that explains what you did? I’d love to try to better understand your setup
Well for PiVPN I just followed the docs to get it setup: https://docs.pivpn.io/
Then I port forwarded the port I use for Wireguard to that same port on my Pi with PiVPN on it.
For Sunshine: https://docs.lizardbyte.dev/projects/sunshine/en/latest/about/installation.html
So now when I want to remotely access my gaming PC, I use Wireguard on my phone, use the configured PiVPN setup on there which points to the domain name that I have setup with my DDNS, then I use a Wake On Lan app setup with my gaming PC’s MAC address to wake it, then I just log into it with Moonlight like normal
Isn’t port forwarding dangerous?
Do you use Linux if so, are you on Wayland ?
Just do it properly and configure sshd securely. When you have a machine exposed to the internet, you should expect it to be attacked. If you really want to give the finger to bots, run endlessh on port 22 and keep sshd on a non-standard port. Stay safe.
endlessh
Lmao thanks for this
10mb is pretty much nothing. May as well just use Fail2Ban.
But it depends on the size of the network/system and how many devices have an open port and are open to connection.
It may not make a difference on 1 server, but if you have a full network with managed switches, routers, firewalls and access points would its impact become more significant?
Not a network expert, just a technician, and I’m curious so any insight is appreciated!
Now try IPv6 only :P
Next time
I get what you say, and you’re definitely not wrong to do it. But as I see it, you only saved ~80Kib of ingress and a few lines of logs in the end. From my monitoring I get ~5000 failed auth per day, which account for less than 1Mbps average bandwidth for the day.
It’s not like it’s consuming my 1Gbps bandwidth or threatening me as I enforce ssh key login. I like to keep things simple, and ssh on port 22 over internet makes it easy to access my boxes from anywhere.
I don’t get why people leave interfaces the public doesn’t need access to open to the public – especially SSH.
Use a VPN if you need access to those interfaces from the “outside”. They’re stupidly easy to set up these days, particularly with Wireguard.
A VPN is easy to setup (and I have it setup by the way), but no VPN is even easier. SSH by itself is sufficiently secure if you keep it up to date with a sane configuration. Bots poking at my ssh port is not something that bother me at all, and not part of any attack vector I want to be secure against.
Out of all the services I expose to the clear web, SSH is probably the one I trust the most.
I would generally agree with this a strong password and SSH without keys has never gone sideways for me and over 15 years of having public Linux servers. but I also make sure to install all security updates on a regular basis on any server no matter what SSH configuration is.
Agreed ! Also it would make graphs pretty boring ;)
Defense in depth – maybe I’m paranoid, but just because something is unlikely doesn’t mean an extra layer of security isn’t advantageous. Particularly when I already have a VPN, so there’s little reason not to use it.
Plus, my logs are easily checked as a side effect.
To each their own ! Security is a complex topic which usually resolves to adjusting the “security/annoyance” cursor to the best position.
In my case the constraints of using a VPN simply outweighs the security benefits.
ssh -p 12345 would leave your boxes accessible from anywhere too. Other blocks of IPs receive 10 times or more requests, as scanners can focus on blocks of ips from major providers.
Yeah I know, I just don’t really care about that traffic to bother changing it :) Also, I’m talking about a server hosted on Hetzner, so I feel like it’s scanned a lot.
And yet it is more likely that tailscale get owned since the reward is much higher. I take my chances with my secured openssh server at port 22 vs a 3rd party company who controlls the access.
Just setup a wireguard system that’s pretty bulletproof
So is SSH
Wireguard doesn’t respond but I agree open-ssh is pretty solid. Can’t speak for any of the other ssh implementations. It can also be poorly configured. Like you could use a password
The benefit of Wireguard is that if you screw it up, it just won’t work. It basically enforces security.
Well, unless you tried to use the original PFSense module.
As others have already said, set up a VPN like wireguard, connect to the VPN and then SSH to the server. No need to open ports for SSH.
I do have port 22 open on my network, but it’s forwarded to an SSH tarpit: https://github.com/skeeto/endlessh
I don’t know if it was mentioned already but how could I check if my ports are under “attack”? OPs graphic looks really nice
Hi, to check attacks you should look at the logs. In this case auth.log. Being attacked on port 22 is not surprising neither really troublesome if you connect via key pair.
My graph was showing egress traffic, on any kind of server the traffic due to these attacks would have been invisible but on a backup server which has (hopefully) only ingress you can clearly see the volume of connections from attackers from bytes teansmitted
Prevent password auth and setup sshguard. Wireguard is very nice in that it doesn’t support password auth.














